How to disable tls 1.2 protocol. TLS protocol in Internet Explorer. SSL TLS protocol
If you are encountering an issue where access to a specific site is failing and a message appears in your browser, there is a reasonable explanation for this. The causes and solutions to the problem are given in this article.
SSL TLS protocol
Users of budgetary organizations, and not only budgetary ones, whose activities are directly related to finance, in interaction with financial organizations, for example, the Ministry of Finance, the Treasury, etc., conduct all their operations exclusively using the secure SSL protocol. Basically, in their work they use Internet browser Explorer. In some cases - Mozilla Firefox.
SSL Error
The main attention when carrying out these operations, and work in general, is paid to the security system: certificates, electronic signatures. Used for work software CryptoPro current version. Concerning problems with SSL and TLS protocols, If SSL error appeared, most likely there is no support for this protocol.
TLS error
TLS error in many cases it can also indicate a lack of protocol support. But... let's see what can be done in this case.
SSL and TLS protocol support
So, when using Microsoft Internet Explorer to visit an SSL-secured website, the title bar displays Make sure ssl and tls protocols are enabled. First of all, you need to enable TLS 1.0 protocol support in Internet Explorer.
If you are visiting a website running Internet Information Services 4.0 or higher, Internet setup Explorer's TLS 1.0 support helps secure your connection. Of course, provided that the remote web server you are trying to use supports this protocol.
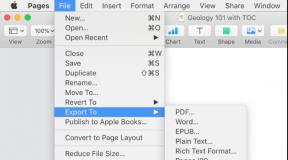
To do this in the menu Service select team Internet Options.
On the tab Additionally In chapter Safety, make sure the following checkboxes are selected:
- Use SSL 2.0
- Use SSL 3.0
- Use SSL 1.0
Click the button Apply , and then OK . Restart your browser .
After enabling TLS 1.0, try visiting the website again.
System Security Policy
If they still occur errors with SSL and TLS If you still can't use SSL, the remote web server probably doesn't support TLS 1.0. In this case, you must disable the system policy that requires FIPS-compliant algorithms.
To do this, in Control panels select Administration, and then double-click Local Security Policy.

In Local Security Settings, expand Local policies, and then click the button Security Settings.
According to the policy on the right side of the window, double click System cryptography: use FIPS-compliant algorithms for encryption, hashing and signing, and then click the button Disabled.

Attention!
The change takes effect when the local security policy is reapplied. Turn it on and restart your browser.
CryptoPro TLS SSL
Update CryptoPro
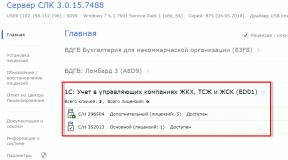
One of the options to solve the problem is to update CryptoPro, as well as configure the resource. In this case, this is working with electronic payments. Go to Certification Authority. Select Electronic Marketplaces as the resource.

After launch automatic settings workplace, there will only be wait for the procedure to complete, then reload browser. If you need to enter or select a resource address, select the one you need. You may also need to restart your computer when setup is complete.
In October, Google engineers published information about a critical vulnerability in SSL version 3.0, which received a funny name POODLE(Padding Oracle On Downgraded Legacy Encryption or poodle 🙂). The vulnerability allows an attacker to gain access to information encrypted with the SSLv3 protocol using a “man in the middle” attack. Both servers and clients that can connect using the SSLv3 protocol are vulnerable to the vulnerability.
In general, the situation is not surprising, because... protocol SSL 3.0, first introduced back in 1996, is already 18 years old and is already morally outdated. In most practical tasks it has already been replaced by a cryptographic protocol TLS(versions 1.0, 1.1 and 1.2).
To protect against the POODLE vulnerability, it is recommended to fully disable SSLv3 support on both client side and server side and henceforth use only TLS. For legacy software users (such as those using IIS 6 on Windows XP), this means they will no longer be able to view HTTPS pages or use other SSL services. If SSLv3 support is not completely disabled and stronger encryption is offered by default, the POODLE vulnerability will still exist. This is due to the peculiarities of choosing and agreeing on the encryption protocol between the client and server, because If problems are detected in the use of TLS, an automatic transition to SSL occurs.
We recommend that you check all your services that may use SSL/TLS in any form and disable SSLv3 support. You can check your web server for vulnerabilities using an online test, for example, here: http://poodlebleed.com/.
Note. It must be clearly understood that disabling SSL v3 at the system-wide level will only work for software that uses system APIs for SSL encryption (Internet Explorer, IIS, SQL NLA, RRAS, etc.). Programs that use their own crypto tools (Firefox, Opera, etc.) need to be updated and configured individually.
Disabling SSLv3 in Windows at the system level
In OS Windows control support for SSL/TLS protocols is provided through the registry.
In this example, we will show how to completely disable SSLv3 at the system level (both client and server level) in Windows Server 2012 R2:
Disable SSLv2 (Windows 2008 / Server and below)
OSes prior to Windows 7 / Windows Server 2008 R2 use an even less secure and outdated protocol by default SSL v2, which should also be disabled for security reasons (in more recent Windows versions, SSLv2 at the client level is disabled by default and only SSLv3 and TLS1.0 are used). To disable SSLv2, you need to repeat the procedure described above, only for the registry key SSL 2.0.

On Windows 2008/2012, SSLv2 is disabled at the client level by default.
Enable TLS 1.1 and TLS 1.2 in Windows Server 2008 R2 and higher
Windows Server 2008 R2 / Windows 7 and higher support TLS 1.1 and TLS 1.2 encryption algorithms, but these protocols are disabled by default. You can enable support for TLS 1.1 and TLS 1.2 in these versions of Windows using a similar scenario

A utility for managing system cryptographic protocols in Windows Server
Exists free utility IIS Crypto, which allows you to conveniently manage the parameters of cryptographic protocols in Windows Server 2003, 2008 and 2012. Using this utility, you can enable or disable any of the encryption protocols in just two clicks.

The program already has several templates that allow you to quickly apply presets for various options security settings.
TLS is a successor to SSL, a protocol that provides a reliable and secure connection between nodes on the Internet. It is used in the development of various clients, including browsers and client-server applications. What is TLS in Internet Explorer?
A little about technology
All enterprises and organizations that engage in financial transactions use this protocol to prevent eavesdropping of packets and unauthorized access by intruders. This technology is designed to protect important connections from attacks by intruders.
Basically, their organizations use a built-in browser. In some cases - Mozilla Firefox.
Enabling or disabling a protocol
It is sometimes impossible to access some sites because support for SSL and TLS technologies is disabled. A notification appears in the browser. So, how can you enable protocols so you can continue to enjoy secure communications?
1.Open Control Panel via Start. Another way: open Explorer and click on the gear icon in the right top corner.
2.Go to the “Browser Options” section and open the “Advanced” block.
3.Check the boxes next to “Use TLS 1.1 and TLS 1.2.”
4.Click OK to save your changes. If you want to disable the protocols, which is highly not recommended, especially if you use online banking, uncheck the same items.
What is the difference between 1.0 and 1.1 and 1.2? 1.1 is only a slightly improved version of TLS 1.0, which partially inherited its shortcomings. 1.2 is the most safe version protocol. On the other hand, not all sites can open with this version of the protocol enabled.
As you know, Skype messenger is directly connected to Internet Explorer as Windows component. If you do not have the TLS protocol ticked in the settings, then problems may arise with Skype. The program simply will not be able to connect to the server.

If TLS support is disabled in Internet Explorer settings, all network-related functions of the program will not work. Moreover, the safety of your data depends on this technology. Do not neglect it if you perform financial transactions in this browser (purchases in online stores, transferring money through online banking or online wallet etc.).
Problem
When trying to log in Personal Area GIIS " Electronic budget» an error message appears:
This page cannot be displayed
Enable TLS 1.0, TLS 1.1, and TLS 1.2 protocols in the " Extra options"and try connecting to the web page https://ssl.budgetplan.minfin.ru again. If you cannot resolve the error, contact your website administrator.
Solution
It is necessary to check the workplace settings according to the document.
The instructions do not mention several nuances:
- You need to install CryptoPro EDS Browser plug-in and check its operation on the demo page.
- It is necessary to disable filtering of the SSL/TLS protocol in the antivirus settings; in other words, for the site you are looking for, you should make an exception for checking a secure connection. It may be called differently in different antiviruses. For example, you need to go to Kaspersky Free “Settings>Advanced>Network>Do not check secure connections” .
The TLS protocol encrypts Internet traffic of all types, thereby making communication and sales online secure. We will talk about how the protocol works and what awaits us in the future.
From the article you will learn:
What is SSL
SSL or Secure Sockets Layer was the original name of the protocol that Netscape developed in the mid-90s. SSL 1.0 was never publicly available, and version 2.0 had serious flaws. SSL 3.0, released in 1996, was a complete overhaul and set the tone for the next phase of development.
What is TLS
When the next version of the protocol was released in 1999, it was standardized by a special working group design of the Internet and gave it a new name: transport layer security, or TLS. As the TLS documentation states, “the difference between this protocol and SSL 3.0 is not critical.” TLS and SSL form an ongoing series of protocols and are often combined under the name SSL/TLS.
The TLS protocol encrypts Internet traffic of any kind. The most common type is web traffic. You know when your browser establishes a TLS connection - if the link in the address bar starts with "https".
TLS is also used by other applications, such as mail and teleconferencing systems.
How TLS works
Encryption is necessary to communicate securely online. If your data is not encrypted, anyone can analyze it and read sensitive information.
The most secure encryption method is asymmetric encryption. This requires 2 keys, 1 public and 1 private. These are files with information, most often very large numbers. The mechanism is complex, but simply put, you can use a public key to encrypt data, but you need a private key to decrypt it. The two keys are connected using a complex mathematical formula, which is difficult to hack.
You can think of a public key as information about the location of a private key. mailbox with a hole, and a private key as the key that opens the box. Anyone who knows where the box is can put a letter there. But to read it, a person needs a key to open the box.
Because asymmetric encryption uses complex mathematical calculations, it requires a lot of computing resources. TLS solves this problem by using asymmetric encryption only at the beginning of a session to encrypt communications between the server and client. The server and client must agree on a single session key, which the two of them will use to encrypt data packets.
The process by which the client and server agree on a session key is called handshake. This is the moment when 2 communicating computers introduce themselves to each other.
TLS handshake process
The TLS handshake process is quite complex. The steps below outline the process in general so you can understand how it works in general.
- The client contacts the server and requests a secure connection. The server responds with a list of ciphers—an algorithmic set for creating encrypted connections—that it knows how to use. The client compares the list with its list of supported ciphers, selects the appropriate one, and lets the server know which one the two of them will use.
- The server provides its digital certificate - electronic document, signed by a third party, which verifies the server's authenticity. The most important information in the certificate is the public key to the cipher. The client confirms the authenticity of the certificate.
- Using the server's public key, the client and server establish a session key that they will both use throughout the session to encrypt communications. There are several methods for this. The client can use the public key to encrypt an arbitrary number, which is then sent to the server to decrypt, and both parties then use that number to establish the session key.
A session key is only valid for one continuous session. If for some reason communication between the client and server is interrupted, a new handshake will be needed to establish a new session key.
Vulnerabilities of the TLS 1.2 and TLS 1.2 protocols
TLS 1.2 is the most common version of the protocol. This version installed the original platform of session encryption options. However, like some previous versions of the protocol, this protocol allowed the use of older encryption techniques to support older computers. Unfortunately, this led to vulnerabilities in version 1.2, as these older encryption mechanisms became more vulnerable.
For example, TLS 1.2 has become particularly vulnerable to tampering attacks, in which an attacker intercepts data packets mid-session and sends them after reading or modifying them. Many of these problems have surfaced over the past 2 years, making it urgent to create an updated version of the protocol.
TLS 1.3
Version 1.3 of the TLS protocol, which will be finalized soon, solves many of the problems with vulnerabilities by abandoning support for legacy encryption systems.
IN new version is compatible with previous versions: For example, the connection will fall back to TLS 1.2 if one of the parties fails to use more new system encryption in the list of allowed protocol algorithms version 1.3. However, in a connection tampering attack, if a hacker forcibly tries to downgrade the protocol version to 1.2 in the middle of a session, this action will be noticed and the connection will be terminated.
How to enable TLS 1.3 support in Google Chrome and Firefox browsers
Firefox and Chrome support TLS 1.3, but this version is not enabled by default. The reason is that it currently only exists in draft form.
Mozilla Firefox
Type about:config into your browser's address bar. Confirm that you understand the risks.
- The Firefox Settings Editor will open.
- Enter security.tls.version.max in search
- Change the value to 4 by doing double click mouse to the current value.


Google Chrome
- Type chrome://flags/ into your browser's address bar to open the experiments panel.
- Find option #tls13-variant
- Click on the menu and set it to Enabled (Draft).
- Restart your browser.
How to check that your browser is using version 1.2
We remind you that version 1.3 is not yet in public use. If you do not want
use the draft, you can stay on version 1.2.
To check that your browser is using version 1.2, follow the same steps as in the instructions above and make sure that:
- For Firefox, the security.tls.version.max value is 3. If it is lower, change it to 3 by double-clicking on the current value.
- For Google Chrome: Click on the browser menu - select Settings- select Show advanced settings- go down to the section System and click on Open proxy settings…:

- In the window that opens, click on the Security tab and make sure that the Use TLS 1.2 field is checked. If not, check it and click OK:

The changes will take effect after you restart your computer.
A quick tool to check your browser's SSL/TLS protocol version
Go to the SSL Labs online protocol version checker tool. The page will show in real time the protocol version used, and whether the browser is susceptible to any vulnerabilities.
Sources: translation